Authorization

Azure DevOps
Prerequisites
Before creating an Azure DevOps credential in Nexla, you need to create a Personal Access Token (PAT) in your Azure DevOps organization. Azure DevOps uses Basic Authentication with Personal Access Tokens for secure API access.
Personal Access Token Setup
Personal Access Tokens provide secure, token-based access to the Azure DevOps API without requiring your account password. PATs can be scoped to specific organizations, projects, and permissions, providing fine-grained access control.
-
Access Azure DevOps: Sign in to your Azure DevOps organization.
-
Navigate to User Settings: Click on your user profile icon in the upper right corner, and select Personal access tokens from the dropdown menu.
-
Create a New Token: Click the + New Token button to create a new Personal Access Token.
-
Configure Token Settings:
- Enter a descriptive name for the token in the Name field (e.g., "Nexla Integration").
- Select the Organization where you want to use this token.
- Set the Expiration date for the token. Tokens can be set to expire after a specific number of days or can be set to never expire (not recommended for security).
- Select the Scopes (permissions) that the token should have. For full API access, select Full access, or select specific scopes based on your needs:
- Work Items (Read & Write): For reading and writing work items
- Code (Read & Write): For reading and writing code repositories
- Build (Read & Execute): For reading and executing builds
- Release (Read, Write & Execute): For reading, writing, and executing releases
- Project and Team (Read): For reading project and team information
- Service Connections (Read & Query): For reading and querying service connections
-
Create and Copy Token: Click the Create button to generate the token. Important: Copy the token immediately after creation, as it will only be displayed once. If you lose the token, you'll need to create a new one.
Personal Access Tokens provide programmatic access to your Azure DevOps organization. Keep your PAT secure and do not share it publicly or commit it to version control systems. If you suspect your token has been compromised, revoke it immediately in the Personal Access Tokens settings and create a new one. For detailed information about creating and managing Personal Access Tokens, see the Azure DevOps Personal Access Tokens documentation.
Create an Azure DevOps Credential
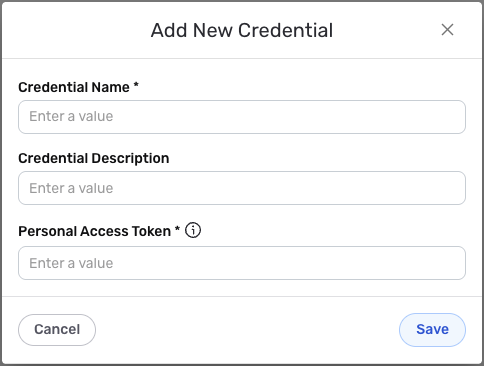
- To create a new Azure DevOps credential, after selecting the data source/destination type, click the Add Credential tile to open the Add New Credential overlay.
New Credential Overlay – Azure DevOps
Credential Name & Description
-
Enter a name for the credential in the Credential Name field and a short, meaningful description in the Credential Description field.
Resource descriptions are recommended but are not required. They should be used provide information about the resource purpose, data freshness, etc. that can help the owner and other users efficiently understand and utilize the resource.
Personal Access Token Configuration
-
Enter your Personal Access Token in the Personal Access Token field. This should be the PAT you created in your Azure DevOps organization. The token is used together with a username for Basic Authentication to the Azure DevOps API.
The Personal Access Token provides secure, token-based access to the Azure DevOps API. The token is used for Basic Authentication, where the username is set to "Nexla" and the password is your Personal Access Token. Keep your PAT secure and do not share it publicly or commit it to version control systems. For detailed information about Azure DevOps API authentication, see the Azure DevOps REST API documentation.
Save the Credential
-
Once all of the relevant steps in the above sections have been completed, click the Save button at the bottom of the overlay to save the configured credential.
-
The newly added credential will now appear in a tile on the Authenticate screen during data source/destination creation and can be selected for use with a new data source or destination.