Authorization

AWS CloudWatch
Prerequisites
Before creating an AWS CloudWatch credential in Nexla, you need to create an IAM user with appropriate permissions and obtain AWS Access Key credentials. AWS CloudWatch uses AWS Signature Version 4 for authentication.
AWS IAM User Setup
The IAM user must have appropriate permissions to access the CloudWatch API. Ensure that the user has the necessary IAM policies attached. For detailed information about CloudWatch API permissions, see the AWS CloudWatch API documentation.
-
Access AWS IAM Console: Sign in to your AWS account and navigate to the IAM Console.
-
Create an IAM User: Create a new IAM user or select an existing user that will be used for API access. This user will need permissions to access the CloudWatch API.
-
Attach CloudWatch Permissions: Attach the necessary IAM policies to the user. The user needs permissions to access the CloudWatch API, such as:
cloudwatch:GetMetricDatacloudwatch:GetMetricStatisticscloudwatch:ListMetricscloudwatch:ListDashboardscloudwatch:PutMetricDatacloudwatch:PutDashboardcloudwatch:GetDashboard- Or attach the
CloudWatchReadOnlyAccessmanaged policy for read-only access, orCloudWatchFullAccessfor full access
-
Create Access Key: Create an access key pair for the IAM user. This will generate an Access Key ID and Secret Access Key that you'll use for authentication.
-
Select AWS Region: Determine which AWS region you want to use for the CloudWatch API. The CloudWatch API is available in all AWS regions. Common regions include
us-east-1(N. Virginia),us-west-2(Oregon),eu-west-1(Ireland), and others. -
Copy Credentials: Copy the Access Key ID and Secret Access Key immediately after creation, as the secret key will only be shown once.
AWS Access Keys provide programmatic access to your AWS account. Keep your Access Key ID and Secret Access Key secure and do not share them publicly or commit them to version control systems. If you suspect your access keys have been compromised, rotate them immediately in the IAM Console. For detailed information about AWS IAM and access keys, see the AWS IAM documentation.
Create an AWS CloudWatch Credential
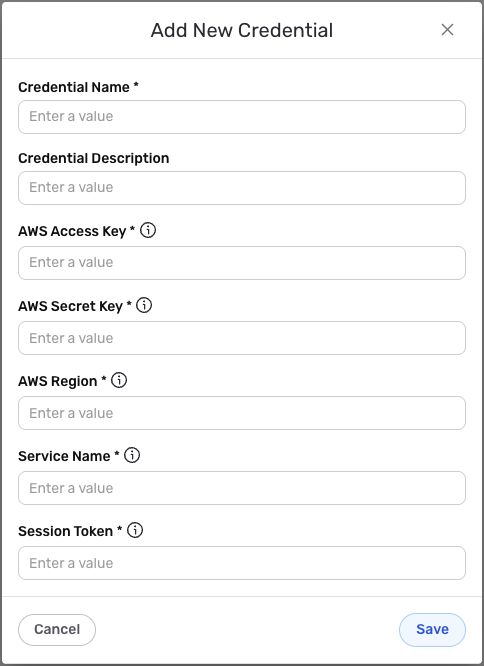
- To create a new AWS CloudWatch credential, after selecting the data source/destination type, click the Add Credential tile to open the Add New Credential overlay.
New Credential Overlay – AWS CloudWatch API
Credential Name & Description
-
Enter a name for the credential in the Credential Name field and a short, meaningful description in the Credential Description field.
Resource descriptions are recommended but are not required. They should be used provide information about the resource purpose, data freshness, etc. that can help the owner and other users efficiently understand and utilize the resource.
AWS Authentication Configuration
-
Enter your AWS Access Key ID in the AWS Access Key field. This should be the Access Key ID obtained from your IAM user's access key pair. The Access Key ID is used together with the Secret Access Key to sign API requests using AWS Signature Version 4.
-
Enter your AWS Secret Access Key in the AWS Secret Key field. This should be the Secret Access Key obtained from your IAM user's access key pair. The Secret Access Key is used together with the Access Key ID to sign API requests.
The AWS Access Key ID and Secret Access Key provide programmatic access to your AWS account through the CloudWatch API. Keep these credentials secure and do not share them publicly or commit them to version control systems. AWS uses AWS Signature Version 4 to sign API requests, which allows Nexla to make authenticated requests to your AWS account.
-
Enter your AWS Region in the AWS Region field. This should be the AWS region where you want to make CloudWatch API requests. Common regions include
us-east-1(N. Virginia),us-west-2(Oregon),eu-west-1(Ireland),ap-southeast-1(Singapore), and others. The CloudWatch API endpoint URL is automatically constructed ashttps://monitoring.{'{region}'}.amazonaws.combased on the region you specify. -
Enter the Service Name in the Service Name field. For AWS CloudWatch, this should be set to
monitoring. The service name is used as part of the AWS Signature Version 4 signing process to identify the AWS service being accessed. -
Optionally, enter a Session Token in the Session Token field if you are using temporary security credentials. Session tokens are required when using temporary credentials from AWS STS (Security Token Service) or when assuming IAM roles. If you are using permanent access keys, you can leave this field empty.
If you are using temporary security credentials (for example, from AWS STS or IAM role assumption), you must provide a Session Token. The session token is added to requests as the
x-amz-access-tokenheader. For permanent access keys, the session token field can be left empty.
Save the Credential
-
Once all of the relevant steps in the above sections have been completed, click the Save button at the bottom of the overlay to save the configured credential.
-
The newly added credential will now appear in a tile on the Authenticate screen during data source/destination creation and can be selected for use with a new data source or destination.