Authorization

Aurora MySQL
Prerequisites
Before creating an Aurora MySQL credential, you'll need to obtain AWS credentials and ensure your Aurora MySQL cluster has the Data API enabled. The AWS RDS Data API uses AWS Signature Version 4 for authentication.
AWS Account Setup
To obtain the required AWS credentials for Aurora MySQL Data API:
-
Sign in to AWS Console: Navigate to https://aws.amazon.com/console/ and sign in to your AWS account. If you don't have an account, you can create one by clicking Create an AWS Account and following the registration process.
-
Access IAM Console: Once signed in, navigate to the AWS Identity and Access Management (IAM) console. You can find this by searching for "IAM" in the AWS services search bar.
-
Create or Use Existing IAM User:
- If you don't have an IAM user with programmatic access, create one:
- Click Users in the IAM console
- Click Add users or Create user
- Provide a username and select Programmatic access as the access type
- Attach policies that grant permissions for RDS Data API access (e.g.,
AmazonRDSDataFullAccessor custom policies with RDS Data API permissions)
- If you already have an IAM user, ensure it has the necessary permissions for RDS Data API
- If you don't have an IAM user with programmatic access, create one:
-
Create Access Keys: For your IAM user:
- Click on the user name in the IAM console
- Go to the Security credentials tab
- Click Create access key
- Select the use case (e.g., "Application running outside AWS")
- Click Create access key
- Important: Copy both the Access key ID and Secret access key immediately. The secret access key is only shown once and cannot be retrieved later.
-
Note AWS Region: Identify the AWS region where your Aurora MySQL cluster is located (e.g.,
us-east-1,us-west-2,eu-west-1). This region will be used in the credential configuration.
AWS access keys are sensitive credentials that provide programmatic access to your AWS resources. Keep these credentials secure and never share them publicly or commit them to version control systems. The access keys are used with AWS Signature Version 4 to authenticate requests to the RDS Data API. For complete information about AWS RDS Data API authentication, see the AWS RDS Data API Documentation.
Aurora MySQL Cluster Configuration
Before using the RDS Data API, ensure your Aurora MySQL cluster has the Data API enabled:
-
Enable Data API: In the AWS RDS console, select your Aurora MySQL cluster and ensure the Data API is enabled. This can be configured during cluster creation or modified in the cluster settings.
-
Obtain Cluster ARN: Note the Amazon Resource Name (ARN) of your Aurora MySQL cluster. This will be needed when configuring data sources.
-
Configure Secrets Manager: The RDS Data API requires database credentials to be stored in AWS Secrets Manager. Ensure you have:
- A secret in AWS Secrets Manager containing your database username and password
- The ARN of the secret (Secret ARN)
API Access Requirements
AWS RDS Data API access requires:
- Valid AWS Account: You must have an active AWS account
- IAM User with Programmatic Access: An IAM user with access keys and appropriate permissions
- AWS Access Key ID: Your IAM user's access key ID
- AWS Secret Access Key: Your IAM user's secret access key
- AWS Region: The region where your Aurora MySQL cluster is located
- Aurora MySQL Cluster: A cluster with the Data API enabled
- Secrets Manager Secret: Database credentials stored in AWS Secrets Manager
The AWS RDS Data API uses AWS Signature Version 4 for authentication. All API requests must use HTTPS and include AWS signature headers.
For complete information about AWS RDS Data API authentication and getting started, see the AWS RDS Data API Documentation.
Create an Aurora MySQL Credential
- To create a new Aurora MySQL credential, after selecting the data source/destination type, click the Add Credential tile to open the Add New Credential overlay.
New Credential Overlay – Aurora MySQL Data API
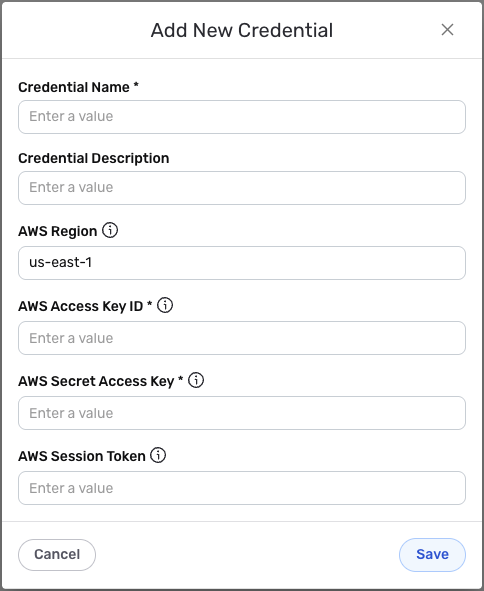
Credential Name & Description
-
Enter a name for the credential in the Credential Name field and a short, meaningful description in the Credential Description field.
Resource descriptions are recommended but are not required. They should be used to provide information about the resource purpose, data freshness, etc. that can help the owner and other users efficiently understand and utilize the resource.
AWS Region Configuration
- AWS Region: Enter the AWS region for your RDS Data API requests in the AWS Region field. The default value is
us-east-1. This should match the region where your Aurora MySQL cluster is located (e.g.,us-east-1,us-west-2,eu-west-1).
AWS Credentials Configuration
-
AWS Access Key ID: Enter your AWS Access Key ID in the AWS Access Key ID field. This is the access key ID from your IAM user's security credentials.
-
AWS Secret Access Key: Enter your AWS Secret Access Key in the AWS Secret Access Key field. This is the secret access key from your IAM user's security credentials.
-
AWS Session Token (optional): If you're using temporary credentials (e.g., from AWS STS), enter the session token in the AWS Session Token field. For permanent IAM user credentials, you can leave this field empty.
The AWS credentials are sensitive information that should be kept secure. Nexla will store these credentials securely and use them only for API authentication purposes. The credentials are used with AWS Signature Version 4 to authenticate requests to the RDS Data API. Ensure your IAM user has the necessary permissions to access the RDS Data API and Secrets Manager.
Save the Credential
-
Once all of the relevant steps in the above sections have been completed, click the Save button at the bottom of the overlay to save the configured credential.
-
The newly added credential will now appear in a tile on the Authenticate screen during data source/destination creation and can be selected for use with a new data source or destination.