Authorization

Jampp
Prerequisites
Before creating a Jampp credential, you need to obtain OAuth2 credentials (Client ID and Client Secret) from your Jampp account. The OAuth2 credentials are required for 2-legged OAuth2 authentication with the Jampp Reporting API.
To obtain your OAuth2 credentials, you need to have a Jampp account and access to the Jampp developer portal or account settings. Once you have access, you can create an application or obtain OAuth2 credentials from your account settings. The Client ID and Client Secret are used for 2-legged OAuth2 authentication, which uses the client credentials flow to obtain an access token. This authentication method is suitable for server-to-server communication where user interaction is not required. The access token is then sent in the Authorization header with the Bearer prefix for all API requests to the Jampp Reporting API. The Jampp Reporting API provides access to advertising performance data, campaign metrics, and reporting information. For detailed information about OAuth2 credential setup, authentication flows, and available API endpoints, refer to the Jampp Reporting API documentation.
Create a Jampp Credential
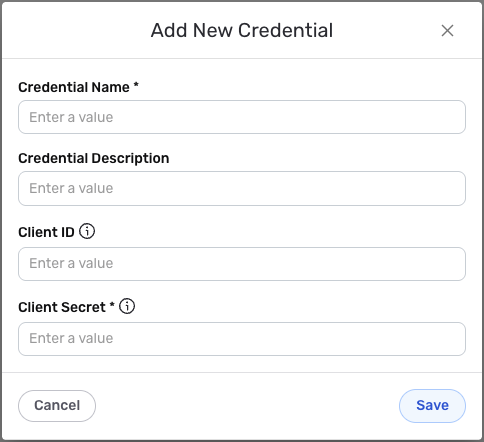
- To create a new Jampp credential, after selecting the data source/destination type, click the Add Credential tile to open the Add New Credential overlay.
New Credential Overlay – Jampp
Credential Name & Description
-
Enter a name for the credential in the Credential Name field and a short, meaningful description in the Credential Description field.
Resource descriptions are recommended but are not required. They should be used provide information about the resource purpose, data freshness, etc. that can help the owner and other users efficiently understand and utilize the resource.
OAuth2 Authentication
Jampp uses 2-legged OAuth2 authentication with the client credentials flow. This authentication method is designed for server-to-server communication where user interaction is not required. The Client ID and Client Secret are used to obtain an access token, which is then used to authenticate API requests to the Jampp Reporting API.
-
Enter your Jampp Client ID in the Client ID field. This is the Client ID you obtained from your Jampp account settings or developer portal. The Client ID is a unique identifier for your application and is used along with the Client Secret to obtain an access token for API authentication. The Client ID is not sensitive and can be shared, but it should be kept secure to prevent unauthorized use.
-
Enter your Jampp Client Secret in the Client Secret field. This is the Client Secret you obtained from your Jampp account settings or developer portal. The Client Secret is used along with the Client ID to obtain an access token for API authentication. The Client Secret is sensitive information and must be kept confidential.
Keep your Client Secret secure and do not share it publicly. The Client Secret provides access to your Jampp account data and should be treated as sensitive information. If your Client Secret is compromised, you should immediately regenerate it in your Jampp account settings. Your Jampp Client Secret can be found in your Jampp account settings or developer portal where you manage your application credentials. The Client Secret is used along with the Client ID to obtain an access token using the 2-legged OAuth2 client credentials flow. Nexla automatically obtains and refreshes the access token as needed. The access token does not expire automatically, but you can regenerate credentials if needed. For detailed information about finding your Client Secret, setting up OAuth2 credentials, and managing access tokens, see the Jampp Reporting API documentation.
Save the Credential
-
Once all of the relevant steps in the above sections have been completed, click the Save button at the bottom of the overlay to save the configured credential.
-
The newly added credential will now appear in a tile on the Authenticate screen during data source/destination creation and can be selected for use with a new data source or destination.